
- DeRisk Center
Risk-based Vulnerability Management
(RBVM)
🏆 Featured in Gartner Market Guide for Vulnerability Assessment Only Indian vendor recognized for innovative vulnerability management
Stop drowning in thousands of vulnerabilities. Start focusing on what actually threatens your business. AI-powered prioritization that reduces security noise by 90% and accelerates remediation by 50%.
Trusted by leading enterprises










- Problem Statement
The Vulnerability Management Crisis
Every CISO Faces
The Reality of Modern Vulnerability Management
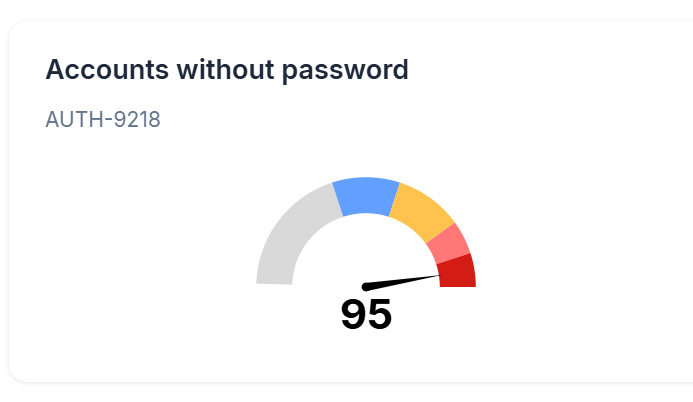
Drowning in Alert Fatigue
- 10,000+ vulnerabilities discovered monthly.
- 95% are noise, 5% are actual business risks.
- Security teams overwhelmed and reactive.
- Critical threats lost in the chaos.
Fragmented Visibility
- Multiple scanners producing isolated reports.
- No unified view across cloud, on-premise, and hybrid environments.
- Inconsistent risk scoring across different tools.
- Manual correlation consuming weeks of effort.
Misaligned Priorities
- Patching based on CVSS scores, not business impact.
- High-severity alerts on non-critical systems.
- Critical business assets with unaddressed medium-risk vulnerabilities.
- No clear ROI on security investments.
Operational Inefficiency
- 3-6 months average remediation cycles.
- 70% of security team time spent on vulnerability triage.
- Endless meetings to prioritize what to fix first.
- Compliance audits revealing the same issues repeatedly.
- SOLUTION OVERVIEW
Seconize RBVM: Intelligence-Driven
Vulnerability Management
Transform your vulnerability program from reactive chaos to proactive risk reduction with AI-powered automation that understands your business context.
Unified Vulnerability Intelligence
- Aggregate and normalize data from 100+ security tools.
- Single pane of glass across all environments.
- Eliminate duplicate findings and false positives.
- Real-time threat landscape visibility.
Business-Context Risk Scoring
- AI algorithms consider asset criticality, network exposure, and threat intelligence.
- Dynamic risk scores that adapt to changing business priorities.
- Prioritization based on actual business impact, not just technical severity.
- Clear guidance on what to fix first for maximum risk reduction.
Automated Remediation Workflows
- Intelligent assignment based on asset ownership and expertise.
- SLA-driven escalation and notification systems.
- Integration with ITSM tools (JIRA, ServiceNow, Remedy).
- Automated verification of remediation effectiveness.
Continuous Risk Monitoring
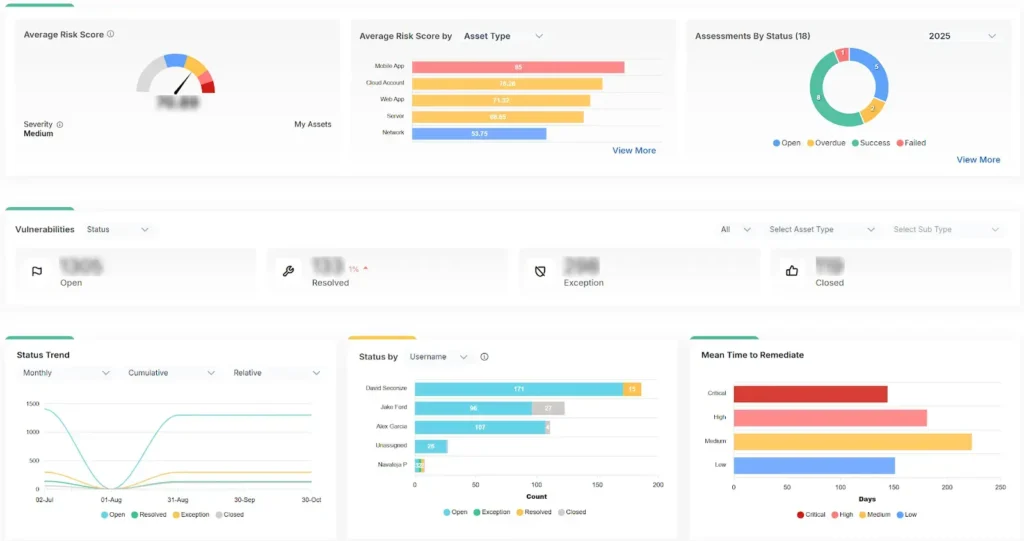
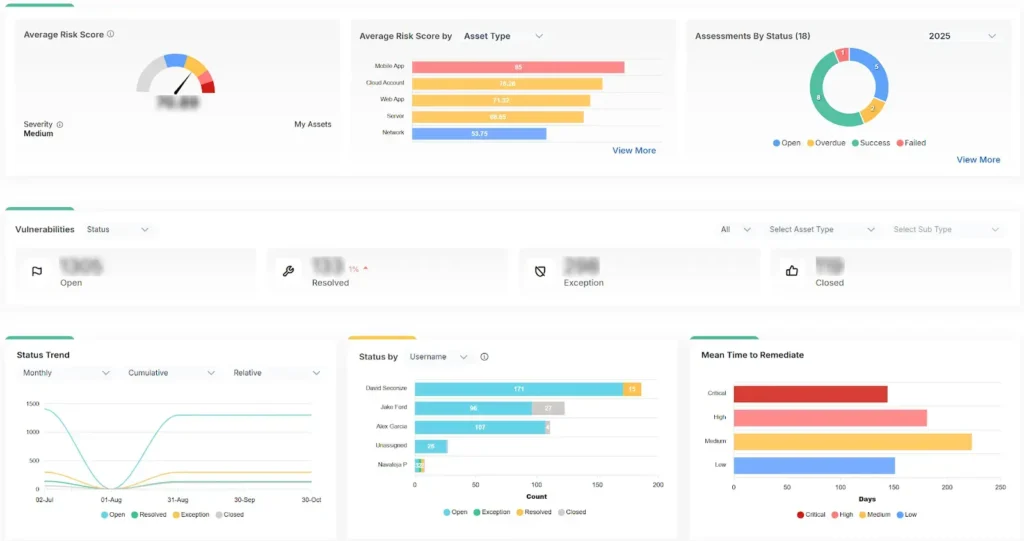
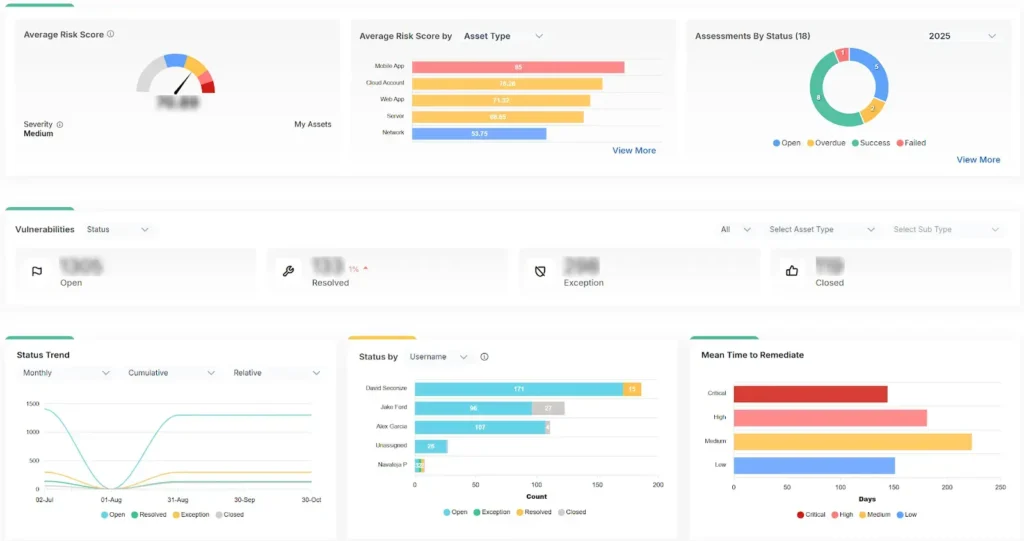
- Real-time risk posture dashboards for executives and security teams.
- Trend analysis and predictive risk modeling.
- Automated compliance reporting for multiple frameworks.
- KPI tracking for security program effectiveness.

- Key Features
Multi-Environment Coverage
- Cloud Infrastructure: AWS, Azure, GCP, OCI security findings.
- On-Premise Systems: Network devices, servers, databases.
- Applications: Web applications, mobile apps, APIs.
- Containers & Kubernetes: Runtime and configuration vulnerabilities.
Intelligent Data Processing
- Automated deduplication across multiple sources.
- Vulnerability correlation and impact analysis.
- Asset relationship mapping and dependency tracking.
- Historical trend analysis and pattern recognition.
100+ Security Tool Integrations
- Vulnerability Scanners: Nessus, Qualys, Rapid7, OpenVAS.
- Cloud Security: AWS Security Hub, Azure Security Center, GCP Security Command Center.
- Application Security: Burp Suite, OWASP ZAP, Checkmarx, Veracode.
- Container Security: Twistlock, Aqua, Sysdig, Anchore.
Advanced Risk Scoring Engine
- Asset Criticality Assessment: Business impact, data sensitivity, user access.
- Network Exposure Analysis: Internet-facing, internal segmentation, lateral movement paths.
- Threat Intelligence Integration: Active exploits, threat actor TTPs, weaponization status.
- Compensating Controls: Existing security measures and their effectiveness.
Customizable Risk Models
- Industry-specific risk frameworks (BFSI, Healthcare, Manufacturing).
- Organizational risk appetite configuration.
- Custom scoring algorithms based on business priorities.
- Integration with existing risk management processes.
Dynamic Prioritization Factors
- Business Impact: Revenue impact, customer data exposure, operational disruption.
- Exploitability: Proof-of-concept availability, exploit complexity, attack vector accessibility.
- Asset Context: System criticality, data classification, network position.
- Threat Landscape: Current attack campaigns, industry-specific threats, geopolitical factors.
Remediation Tracking & Validation
- Real-time remediation status monitoring.
- Automated verification through re-scanning.
- Exception management with approval workflows.
- Remediation effectiveness measurement and reporting.
Smart Assignment & Workflows
- Automated ticket creation in ITSM systems (JIRA, ServiceNow, Remedy).
- Intelligent assignment based on asset ownership and technical expertise.
- SLA-driven escalation with customizable notification rules.
- Bulk remediation workflows for similar vulnerabilities across multiple assets.
Integration Capabilities
- ITSM Integration: Seamless ticket lifecycle management.
- Configuration Management: Integration with CMDB systems.
- Patch Management: Coordination with patch deployment tools.
- Change Management: Automated change request generation.
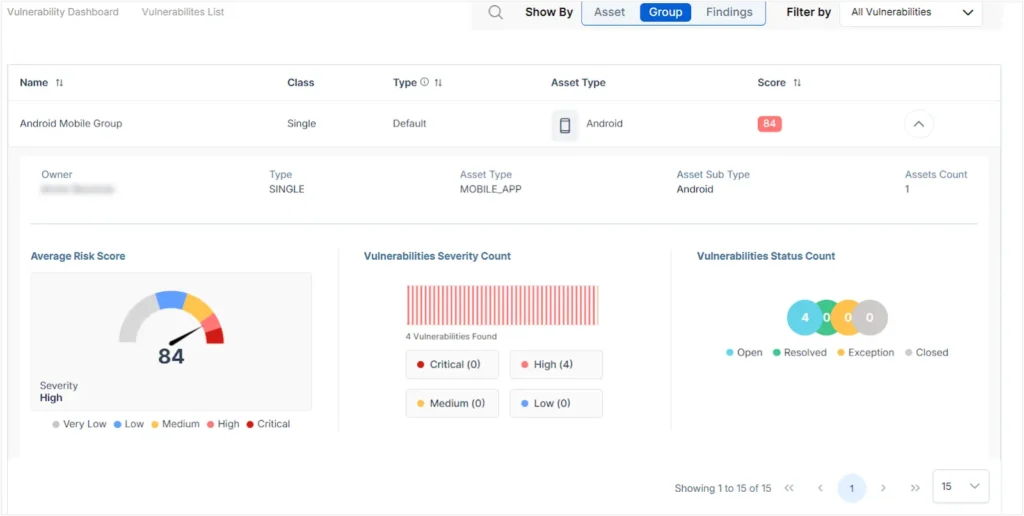
Operational Dashboards
- Vulnerability Aging: Time-to-remediation tracking by severity and asset type.
- Team Performance: Individual and team productivity metrics.
- SLA Compliance: Remediation timeline adherence and exception tracking.
- Asset Risk Heatmaps: Visual representation of risk distribution across the environment.
Executive Risk Dashboards
- Enterprise Risk Score: Single metric representing overall security posture.
- Risk Trend Analysis: Historical and predictive risk trajectory.
- Business Impact Assessment: Potential financial and operational impact.
- Remediation ROI: Cost-benefit analysis of security investments.
Compliance Reporting
- Automated reports for ISO 27001, SOC 2, PCI DSS, NIST frameworks.
- Regulatory reporting for BFSI (RBI, SEBI), Healthcare (HIPAA), and other industries.
- Custom report templates with scheduled distribution.
- Audit trail documentation for compliance validation.
- BUSINESS BENEFITS
Measurable Business
Impact of
RBVM


Cost Reduction & Efficiency Gains
- 50% faster vulnerability remediation cycles.
- 90% reduction in security team triage effort.
- 70% decrease in false positive investigations.
- 60% reduction in emergency patching incidents.
Risk Reduction & Security Improvement
- 80% improvement in critical vulnerability remediation times.
- 95% reduction in vulnerability-related security incidents.
- 75% improvement in security posture measurement accuracy.
- 85% increase in proactive threat mitigation.
Operational Excellence
- Single source of truth for vulnerability data across all environments.
- Automated compliance reporting reducing audit preparation time by 80%.
- Clear ROI measurement for security investments and resource allocation.
- Strategic security planning based on data-driven risk insights.
Competitive Advantage
- Faster time-to-market for new products with integrated security.
- Enhanced customer trust through demonstrable security posture.
- Regulatory compliance confidence with continuous monitoring.
- Optimized security spending with risk-based investment decisions.
- Testimonials
What Our Customers Say

Customer

Sindhu Raghavendra
QA Manager – I.AM+
I am very impressed with how the team from Seconize has worked with our team. They were highly professional and the entire process went smoothly. Seconize was prompt with all the tasks right from the beginning.

Seconize DeRisk Center
“Overall experience with Seconize has been good till date. We have been using the platform for almost a year now. Overall Support from the team is good.”
Manager, IT Security and Risk Management - Manufacturing
Customer

Jayanth Ravindran
Head, Product & Technology – FINVISAGE
We chose Seconize for penetration testing and security guidance, impressed by the founders’ relevant experience. Their team was proactive, enthusiastic, and provided valuable insights.

Seconize DeRisk Center
“We had a pleasant overall experience. The requirements were gathered professionally and precisely, communication was on point, and the implementation and use of the product was seamless and pain-free.”
Chief Information Security Officer - Healthcare and Biotech

Seconize DeRisk Center
“Best Al based tool which helps in Vulnerability and Compliance management to comply with Audit.”
IT Manager - Banking

Seconize DeRisk Center
“It brings all the risks together in one place and quickly updates the risk scores. The automation feature saves a lot of time and the reports are crisp and clear.”